AEC data is sensitive: blueprints, models, costs, and client details. A single leak can hurt bids, delay permits, and damage trust. Remote work adds new access points. This guide shows what’s at risk, why data security for virtual assistants is important, where virtual assistants touch your CDE and PM tools, and the controls that actually cut exposure. We reference ISO 19650, Autodesk security, and current breach stats so you can act with confidence. Ransomware and social engineering keep rising; the FBI logged $16.6B in losses in 2024 (FBI IC3, 2024). MFA blocks the vast majority of account takeovers, ~99% according to Microsoft’s data, so identity controls come first.
Why Data Security Matters in the AEC Industry?
Global cybercrime costs are projected to top $9 trillion in 2024, up from about $1 trillion before the pandemic. The massive shift to digital operations over the past five years has transformed how businesses function. AEC data is far more sensitive than many realize. Virtual assistants and remote staff often handle:
- Architectural blueprints and engineering drawings stored in BIM 360 or ACC.
- Cost estimates, project budgets, and client contracts.
- RFIs, submittals, and documentation tied to regulated environments like healthcare or federal projects.
Even a single data leak could lead to lost bids, contract penalties, or violations of GDPR/CPRA and HIPAA if client data is involved. According to Verizon’s findings, nearly seven out of ten customers say they’d stop doing business with a company that experienced a data breach.
Remote work multiplies access paths. Virtual assistants may use your Autodesk Construction Cloud (ACC/BIM 360), Google Workspace, or Procore.
That’s fine, if permissions are tight and monitored. Autodesk publishes ISO 27001 and related attestations for ACC; use them, but still apply least-privilege and audits on your side.
Why AEC Firms Face Unique VA Risks?
AEC workflows blend technical, financial, and design data, all flowing through shared platforms. That mix makes remote collaboration efficient but risky.
What’s at Stake: BIM Files, Client PII, Bids, and CDE Data
A typical architectural virtual assistant may handle DWG, RVT, or IFC files; a project coordinator might access client lists or proposal data. Attackers know this. These assets often live inside your Autodesk Construction Cloud, Procore, or Bluebeam environments.
A simple permission error could expose sensitive drawings or contractual details across multiple teams or vendors.
Where VAs Touch Data in ACC/BIM 360 and Procore
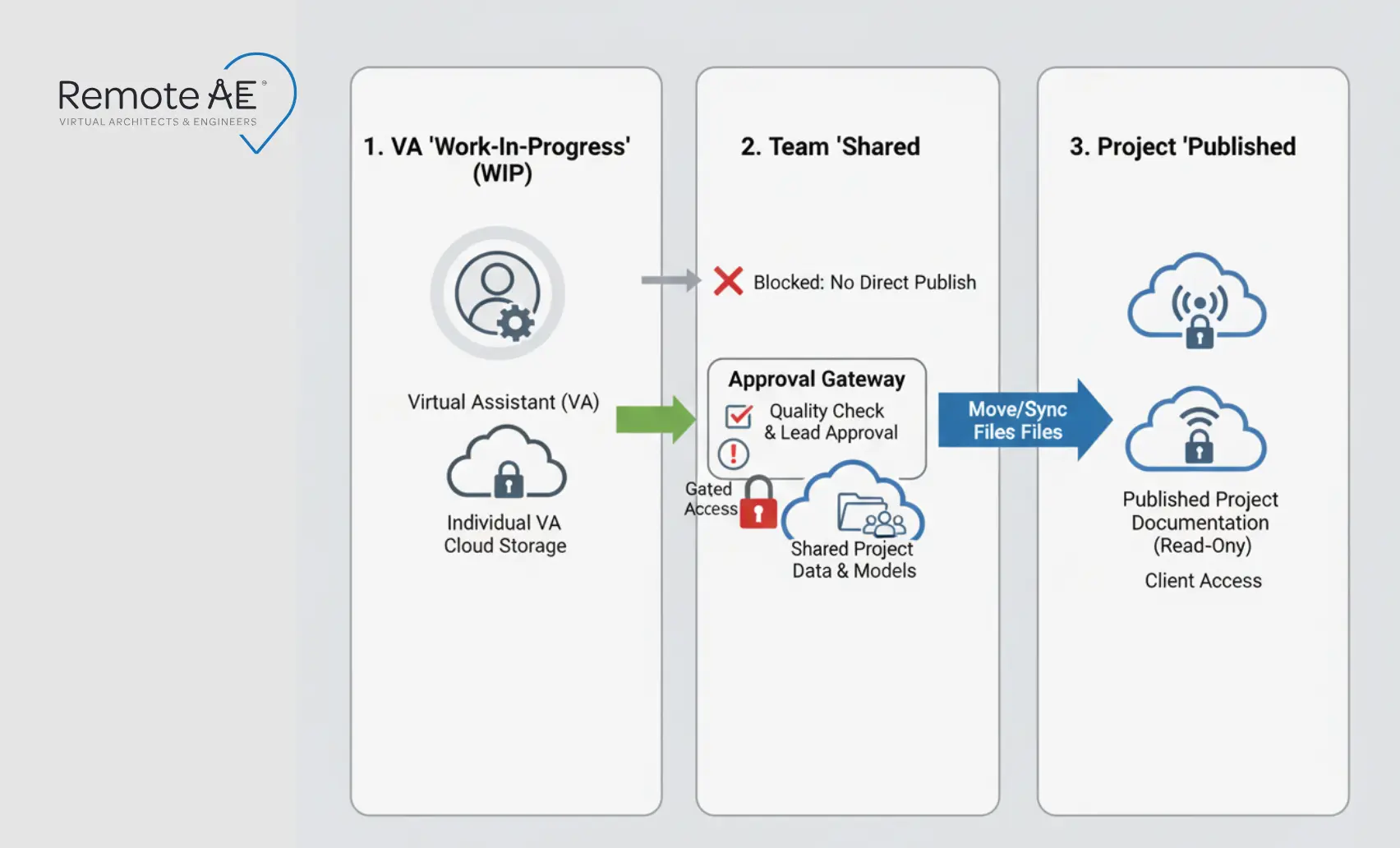
Map permissions to ISO 19650-style states: WIP → Shared → Published. Give virtual assistants Contributor rights only where needed, block Admin on sensitive containers, and require approvals before anything reaches Published. Log all uploads, shares, and Issues.
For Procore, require MFA and limit project-level roles to the minimum required for RFIs, submittals, or document control (Procore MFA guidance). ISO 19650 guidance from the UK BIM Framework explains state-based control and why it reduces leakage and version drift.
Data Security Risks with Virtual Assistants
Remote work introduces new attack surfaces, especially when external assistants manage daily operations inside your AEC project environments. While virtual assistants strengthen productivity, without clear access controls and compliance policies, they can also become weak points in your data security posture.
Let’s break down the most common risks AEC firms face, and how to counter them.
Unauthorized Access
Remote assistants can accidentally see folders they don’t need, WIP archives, bid numbers, and even HR docs. The fix is role-based access control tied to ISO-style states (WIP → Shared → Published) and least-privilege roles in Autodesk Construction Cloud and Procore. Review permissions monthly and log every “share” event. Autodesk documents its cloud compliance posture, but you still set the gates on your side.
What to do now
- Map every VA role to a Contributor scope; restrict Admin.
- Require approvals to move files from WIP to Shared/Published.
- Turn on access logs and review them on a cadence.
For extra security, integrate VPN and SSO (Single Sign-On) systems so that every contractor’s access is logged and auditable.
Phishing and Social Engineering
Virtual assistants are often targeted by phishing campaigns that mimic internal emails or construction platforms like Procore. Attackers exploit trust to collect login credentials or insert malicious links.
Preventive measures include:
- Mandatory cyber awareness training for all contractors.
- Using email DLP (Data Loss Prevention) filters in Google Workspace or Microsoft 365.
- Configuring SOC 2-aligned incident response plans for quick containment if credentials are compromised.
Even one phishing click can expose sensitive RFIs, submittals, or project bids stored in your CDE (Common Data Environment), so proactive awareness is non-negotiable.
Cloud and File-Sharing Vulnerabilities
Public links, personal drives, and unmanaged exports create leakage. Keep project files inside your CDE or business drives and use expiring, access-scoped links.
Enable encryption at rest/in transit and versioning for roll-backs. Autodesk’s Trust Center outlines security and certifications; align your settings accordingly.
What to do now
- Disable public links; use time-boxed, user-scoped shares.
- Keep official files in ACC/Docs or business drives (OneDrive, Egnyte, Dropbox Business) with versioning.
- Snapshot model milestones; test restores monthly.
Cloud security aligns with CIS Controls, which recommend encryption, continuous monitoring, and secure configuration for every external user.
Client Data Mismanagement
PII in contracts or change orders demands care. Use NDAs, data handling policies, and approve any export of client information. IC3 reports $16.6B in cybercrime losses in 2024; mishandled data raises legal and financial exposure.
What to do now
- Require NDAs; restrict PII to labeled folders with stricter roles.
- Ban personal email for project content.
- Add a “PII present?” checkbox to submittals.
AEC Compliance Notes You Can’t Skip
AEC firms must meet strict documentation and access standards for both internal control and project eligibility. Let’s review the most relevant compliance frameworks.
ISO 19650 and Your CDE Permissions
Under ISO 19650, every user in a Common Data Environment (CDE) must have controlled access. Virtual assistants handling RFIs, takeoffs, or sheet sets should only work within their defined permission zone.
Assign project-level access in ACC or BIM 360 based on role categories, such as Document Control or Design Coordination. This verifies traceability for every file action.
CMMC/ITAR Flags for Federal Work
If your projects involve federal clients, the Cybersecurity Maturity Model Certification (CMMC) or ITAR requirements may apply.
When outsourcing, restrict remote access to U.S.-based assistants or ensure data never leaves approved cloud environments. Partner only with vendors who follow CISA and NIST cybersecurity guidance.
Best Practices for AEC Firms When Working with Virtual Assistants
Your firm’s data security isn’t just about tools; it’s about consistent processes and disciplined oversight. The following best practices help reduce risk while keeping productivity high.
- Use secure communication tools like Microsoft Teams, Slack Enterprise, or encrypted email for sensitive project discussions.
- Define data-sharing boundaries before project kickoff; determine which systems (ACC, Procore, BIM 360) a VA can access.
- Keep sensitive project files in restricted directories with version control and audit trails.
- Regularly review access permissions, especially after project completion or staff turnover.
- Create a backup and disaster recovery plan (3-2-1 pattern) with daily automated syncs to secure cloud storage.
- In Procore, enable org-wide MFA; Procore documents setup and enforcement steps.
Tools and Technologies That Protect Data
Technology is the backbone of secure AEC operations. The right mix of authentication, encryption, and monitoring tools guarantees that your virtual assistants can work productively while keeping sensitive project data safe.
Multi-Factor Authentication & Passkeys
Every external login should be gated behind MFA (Multi-Factor Authentication) or FIDO Alliance passkeys. This simple step drastically reduces credential theft and unauthorized access.
- Enforce MFA across Autodesk Construction Cloud (ACC), Procore, and Google Workspace.
- Use Device Bound Session Credentials to tie each login to a verified device.
- Replace shared passwords with password managers (like 1Password or Bitwarden) for secure, auditable access.
With Zero Trust as outlined in NIST SP 800-207, each user and device is continuously verified, not just once during sign-in.
Password Managers & Secrets Sharing
AEC projects often involve multiple contractors logging into shared environments. Instead of sending credentials via chat or email, use encrypted password managers with role-based vaults.
- Grant temporary, revocable access for virtual assistants.
- Use least-privilege principles for each tool, ensuring contractors see only what’s necessary.
- Implement centralized logging for every credential access event.
Secure File Sharing and Backup Solutions
Files are the lifeblood of architecture and engineering projects, from BIM models to RFIs. Protect them at every stage with:
- Encrypted cloud drives (Egnyte, OneDrive for Business, Dropbox Business).
- Regular automated backups and version control in BIM 360 or ACC Docs.
- Cloud Access Security Broker (CASB) or Secure Service Edge (SSE) tools for real-time threat monitoring.
This approach aligns with CIS Controls 11–13, emphasizing secure data transmission, backup, and recovery.
How to Choose a Secure Virtual Assistant Partner?
Outsourcing is only safe if your partner has a proven security foundation. Before hiring, AEC firms should conduct due diligence to verify compliance and maturity.
Ask potential providers:
- What security protocols do you follow? Look for written policies covering MFA, RBAC, device control, backups, and incident response.
- How do you train staff? Ask for a security-awareness program with phishing simulations and tool-specific SOPs.
- What’s your incident response plan? Expect a documented first-24-hours playbook (containment, comms, restore).
- How is access granted and revoked? You want SSO + just-in-time roles, with a 15-minute offboarding checklist.
- Do you sign NDAs and DPAs? Contracts should name data types, retention, and breach notification timelines.
- Can you align with the ISO 19650 CDE states? Confirm WIP → Shared → Published gates and approvals.
- Do you support logs and audits? You should be able to review shares, downloads, and Issues weekly.
Red flags:
- No written security policies or access logs.
- Lack of dedicated compliance oversight.
- Unrestricted access to client systems or project databases.
Verification steps
- Run a 2-week pilot: smallest viable scope, read-only where possible.
- Inspect their SOP pack (naming, stamps, exports).
- Require a security checklist to be signed at kickoff and weekly.
- Confirm device posture: disk encryption, EDR, screen-lock, and OS patching.
- Test the offboarding drill, revoke, rotate, and archive in 15 minutes.

Choose a Reputable Virtual Assistant from Remote AE
Remote AE combines 15+ years of AEC staffing experience with SOC 2-aligned infrastructure. Every assistant is vetted, trained, and onboarded under strict confidentiality and least-privilege access policies.
When you partner with Remote AE, you gain more than skilled AEC support; you gain peace of mind. Each assistant is trained in data handling, file version control, and role-based permissions, verifying your project information stays protected from day one.
Even if it’s managing RFIs, updating takeoffs, or supporting BIM coordination, your Remote AE assistant follows Zero Trust principles across every action.
Keep Your Data Safe While Scaling Your Team!
Don’t compromise data security for productivity. Work with a trusted partner that understands both AEC operations and cybersecurity. Contact Remote AE today to discuss your project needs and onboard a virtual assistant who meets the highest standards of confidentiality, compliance, and professionalism.
Frequently Asked Questions
What’s the best way to manage 2FA for a VA?
Use app-based 2FA through tools like Authy or Microsoft Authenticator. For shared access, password managers can generate temporary 2FA tokens. Avoid SMS-based verification. Assign recovery contacts internally to prevent lockouts if the VA’s device fails.
Do VAs need to sign an NDA? What must it include?
Yes. An NDA should cover data confidentiality, IP ownership, client privacy, and non-disclosure duration. It ensures your business and client information remains protected. Always require the VA to sign before granting any platform or document access.
What is a BAA, and when is it required?
A Business Associate Agreement (BAA) is required when a VA handles protected health information (PHI) under HIPAA. It defines each party’s security obligations and legal responsibilities. You’ll need one if your firm serves healthcare or government-related clients.
What tools reduce risk when VAs work on public Wi-Fi?
Require VPN connections, device encryption, and MFA. Tools like NordLayer, Perimeter 81, or Cisco AnyConnect protect sessions on public networks. Disable auto-connect and ensure your VA’s device runs current antivirus and OS updates.


